Master Cybersecurity Compliance Workflow for UK SMEs
- Gary Sinnott

- Feb 8
- 8 min read

Facing mounting regulatory expectations can feel daunting, especially as cyber breaches grow more frequent across British fintech firms. For Compliance Officers at UK-based SMEs, achieving robust security standards is not just regulatory box-ticking but a strategic move for winning B2B contracts. This guide unpacks practical steps for implementing ISO 27001:2022, using a risk-based approach and highlighting how phishing remains the most disruptive attack vector for UK businesses according to the latest Government survey.
Table of Contents
Quick Summary
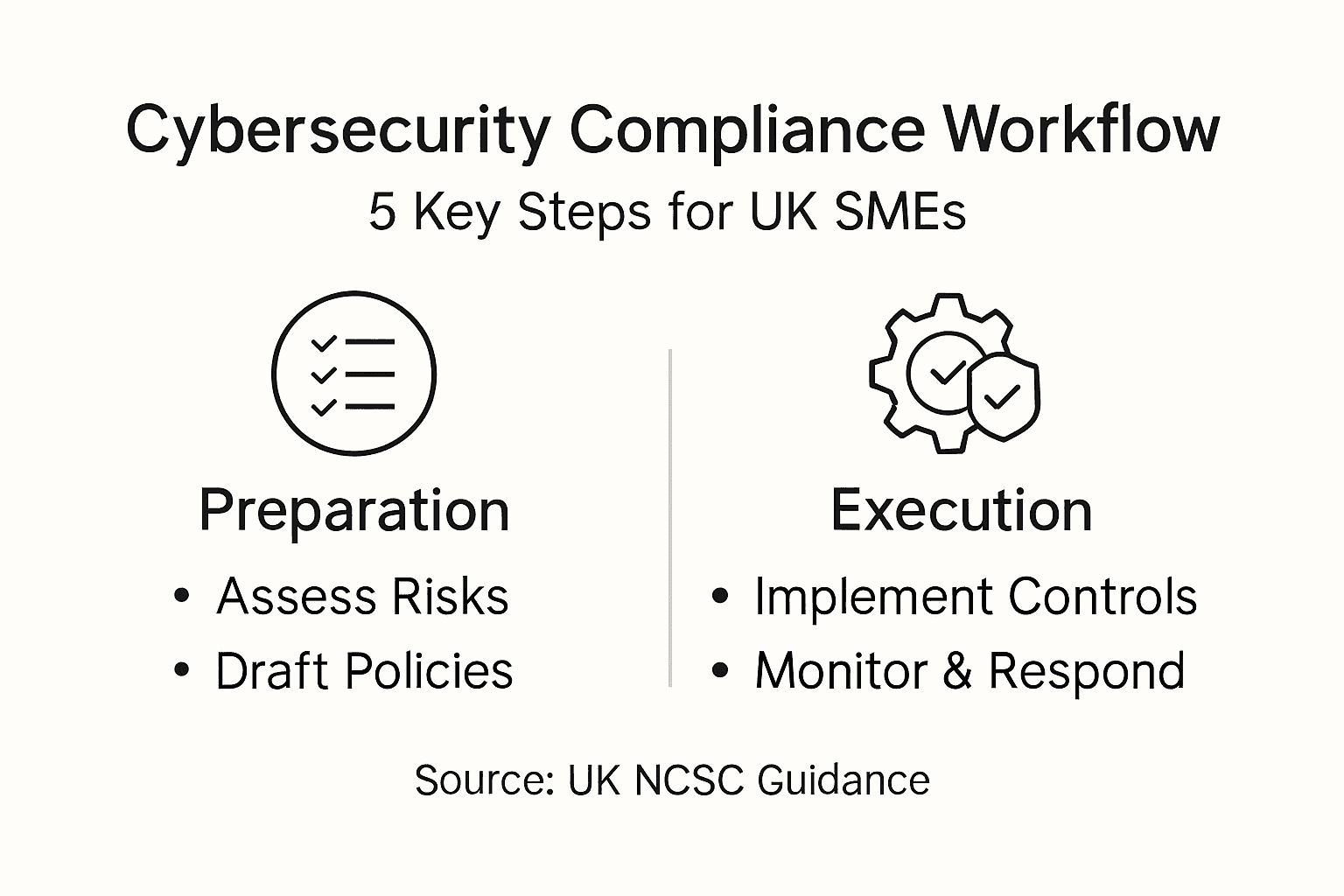
Key Insight | Explanation |
1. Conduct comprehensive risk assessments | Identify vulnerabilities in your digital infrastructure to prioritise and mitigate potential cyber threats effectively. |
2. Develop tailored security policies | Create comprehensive security policies aligned with your organisation’s risk profile and operational requirements for effective defence. |
3. Implement strategic technical controls | Use multi-layered security controls like multi-factor authentication and access control to protect digital assets. |
4. Maintain ongoing monitoring practices | Establish continuous monitoring and incident management to quickly detect, respond to, and learn from security incidents. |
5. Ensure meticulous compliance documentation | Keep detailed records of security policies and audits to demonstrate compliance and track your organisation’s security maturity. |
Step 1: Assess organisational risks and compliance gaps
Successfully navigating cybersecurity compliance begins with a comprehensive risk assessment that reveals potential vulnerabilities in your organisation’s digital infrastructure. Your goal is to identify and prioritise potential cyber threats before they become critical security challenges.
To conduct an effective risk assessment, start by mapping your entire digital ecosystem. This involves creating a detailed inventory of all hardware, software, networks, and data storage systems. Critical cyber risk mapping helps SMEs understand their unique threat landscape and potential compliance gaps.
Key steps in your risk assessment include:
Catalogue all digital assets and data repositories
Identify current security controls and policies
Evaluate potential vulnerabilities in each system
Assess the potential impact of different cyber threats
Review historical incident data and near-misses
Comprehensive risk assessment isn’t just a compliance checkbox - it’s your organisation’s strategic defence blueprint.
While conducting your assessment, pay close attention to the most prevalent threats. According to the Cyber Security Breaches Survey, phishing remains the most disruptive attack vector for UK businesses. Understanding these common threats helps prioritise your mitigation strategies.
The following table compares common cyber threats for UK SMEs and their typical business impacts:
Cyber Threat | Attack Method | Business Impact |
Phishing | Deceptive emails | Data breaches, financial loss |
Ransomware | Malicious encryption | Operational downtime, extortion |
Supply Chain Risk | Compromised partners | Loss of trust, regulatory penalties |
Insider Threats | Unauthorised actions | Data leaks, reputational damage |
Prioritise risks based on their potential business impact. Not all vulnerabilities are created equal - focus on those that could cause significant operational disruption or financial damage.
Top tip: Document every step of your risk assessment process meticulously, creating a clear audit trail that demonstrates your proactive approach to cybersecurity governance.
Step 2: Design tailored security policies and framework adoption
Building a robust cybersecurity strategy requires developing comprehensive security policies that align precisely with your organisation’s unique risk profile and operational requirements. This critical step transforms generic guidelines into a custom defence mechanism tailored specifically for your SME’s digital ecosystem.
Security frameworks for SMEs provide structured guidance for creating systematic security approaches. Start by mapping your organisational requirements against established international standards such as ISO/IEC 27001 and NIST guidelines. This approach ensures your policies are both comprehensive and adaptable to your specific business context.
Here is a summary of how leading security frameworks support SME cybersecurity efforts:
Framework | Main Strength | Alignment for SMEs |
ISO/IEC 27001 | Holistic risk-based approach | Sets clear controls and policies |
NIST CSF | Flexible practical guidelines | Adaptable for organisation needs |
Cyber Essentials | UK-focused baseline security | Simple certification route |
Key elements to include in your security policy framework:
Define clear security roles and responsibilities
Establish data protection and access control protocols
Create incident response and breach notification procedures
Outline employee security training requirements
Develop vendor and third-party risk management guidelines
A well-designed security policy is not just documentation - it’s your organisation’s digital immune system.
Align your policies with the UK Government’s cybersecurity recommendations, focusing on creating a dynamic and adaptable security framework. This means regularly reviewing and updating your policies to reflect emerging threats and technological changes.
Prioritise practical implementation over bureaucratic complexity. Your security policies should be clear, concise, and actionable, enabling your team to understand and follow them effectively.
Top tip: Involve team members from different departments when drafting security policies to ensure comprehensive coverage and better organisational buy-in.
Step 3: Implement technical and procedural controls strategically
Transforming your cybersecurity strategy from theoretical framework to practical defence requires methodical implementation of both technical and procedural controls. Your goal is to create a comprehensive security ecosystem that protects your organisation’s digital assets while remaining flexible and responsive to emerging threats.
Cyber Security Codes of Practice provide essential guidance for developing robust security controls. Focus on implementing a multi-layered approach that addresses technological vulnerabilities and human factors simultaneously.
Key technical and procedural controls to prioritise:
Implement multi-factor authentication
Develop comprehensive patch management protocols
Create granular access control mechanisms
Establish continuous monitoring systems
Design robust data encryption strategies
Implement network segmentation techniques
Strategic control implementation transforms cybersecurity from a burden into a competitive advantage.
Configure access controls with precision, ensuring employees have exactly the permissions required for their roles. This principle of least privilege minimises potential breach points and reduces organisational risk.
Consider each control as an interconnected component of your broader security strategy. Technical solutions like firewalls and encryption must be complemented by procedural controls such as regular security awareness training and incident response planning.
Top tip: Conduct periodic penetration testing to validate the effectiveness of your implemented controls, treating them as dynamic safeguards rather than static checkboxes.
Step 4: Maintain ongoing monitoring and incident management
Establishing a proactive cybersecurity strategy requires continuous vigilance and a systematic approach to detecting, responding to, and learning from potential security incidents. Your organisation needs a dynamic monitoring framework that adapts quickly to emerging threats and minimises potential damage.
Cyber incident response strategies are essential for maintaining organisational resilience. Develop a comprehensive incident management plan that outlines clear protocols for identifying, containing, and mitigating security breaches.
Key components of an effective monitoring and incident management strategy:
Implement real-time security information and event monitoring
Establish clear incident classification and escalation procedures
Create detailed forensic logging and analysis capabilities
Design automated threat detection mechanisms
Develop comprehensive incident response workflows
Conduct regular security awareness training
Effective incident management transforms potential cyber catastrophes into manageable challenges.
Configure monitoring tools to provide granular visibility across your entire digital ecosystem. This means tracking network traffic, user activities, system logs, and potential anomalies that could indicate a security threat.
Regular review and updating of your incident response plan is crucial. Technology and threat landscapes evolve rapidly, so your monitoring strategy must remain adaptive and responsive.
Top tip: Schedule quarterly tabletop exercises to simulate cyber incident scenarios, ensuring your team remains prepared and your response mechanisms stay sharp.
Step 5: Verify compliance with audits and documentation
Successfully demonstrating your cybersecurity compliance requires meticulous documentation and strategic audit preparation. Your objective is to transform compliance from a bureaucratic exercise into a credible narrative of your organisation’s security maturity.
Cyber security documentation standards provide crucial guidance for maintaining comprehensive audit trails. Systematic documentation not only proves your regulatory adherence but also serves as a strategic tool for continuous improvement.
Key elements to prepare for compliance verification:
Maintain detailed security policy documentation
Create comprehensive incident response logs
Develop clear evidence of control implementation
Compile risk assessment and mitigation records
Document staff security awareness training
Prepare system configuration and change management records
Compliance documentation is your organisational security passport - treat it with precision and care.
Organise your documentation systematically, ensuring each policy and procedure is current, accessible, and clearly linked to specific security controls. This approach transforms documentation from a static record to a dynamic management tool.
Prepare for both internal and external audits by developing a robust evidence management system. Your documentation should tell a coherent story of proactive risk management and continuous security enhancement.
Top tip: Implement a digital document management system that automatically tracks version changes and provides instant audit trail capabilities.
Elevate Your Cybersecurity Compliance from Checklist to Competitive Edge
UK SMEs face the challenge of transforming complex cybersecurity requirements into practical, actionable strategies that protect business interests and enable growth. This article highlights crucial steps such as risk assessment, tailored policy design, and ongoing monitoring - all essential for turning compliance into a strong market differentiator. Yet without the right support, navigating frameworks like ISO 27001, Cyber Essentials, and continuous vulnerability management can feel overwhelming.
Freshcyber offers a strategic partnership designed specifically to meet these challenges head-on. Through our vCISO-led Compliance services, we provide expert leadership in framework implementation, dynamic risk and policy management, and seamless audit readiness. Combined with our 24/7 Managed Detection and Response and focussed Vulnerability Management programmes, we empower your organisation to not only meet but exceed cybersecurity standards - giving you the confidence to win larger contracts and scale securely.

Take the step from simply managing compliance to owning it as your most valuable business asset. Explore how Freshcyber can help you build a resilient cybersecurity posture uniquely tailored for UK SMEs. Visit Freshcyber today and start your journey towards true digital resilience.
Frequently Asked Questions
How do I conduct a risk assessment for cybersecurity compliance in my SME?
Start by creating a comprehensive inventory of all hardware, software, networks, and data storage systems in your organisation. Prioritise potential vulnerabilities by assessing the impact of various cyber threats within 30 days to establish a solid foundation for your cybersecurity strategy.
What key elements should be included in my cybersecurity policy framework?
Your cybersecurity policy framework should encompass clear security roles, data protection protocols, incident response procedures, employee training requirements, and vendor risk management guidelines. Develop and implement these policies within the next 60 days to ensure they align with your specific organisational needs.
How can I effectively implement technical controls for cybersecurity?
Focus on deploying controls such as multi-factor authentication, robust patch management, and continuous monitoring systems. Implement these measures systematically, aiming to establish a multi-layered security approach within three months to better protect your digital assets.
What is the best way to manage incidents and monitor cybersecurity continuously?
Create a dynamic incident management plan that includes real-time monitoring, clear escalation procedures, and ongoing security training. Establish these components within 45 days to ensure your organisation can respond swiftly to potential security incidents.
How should I prepare for cybersecurity compliance audits?
Maintain detailed documentation of security policies, incident response logs, and evidence of control implementation. Prepare these documents systematically in advance of audits to facilitate a smooth compliance verification process within 60 days.
Recommended
Comments