Vulnerability Scanning Explained: Key Benefits for SMEs
- Gary Sinnott

- Nov 19, 2025
- 7 min read

Most cyber attacks exploit security flaws that could have been fixed with routine checks. Keeping your business safe means staying ahead of invisible threats that lurk in networks, software, and devices. Over 70 percent of data breaches begin with unpatched vulnerabilities, putting sensitive information and company reputation at risk. Understanding vulnerability scanning helps you spot weak points early and protect your digital assets so problems never turn into crises.
Table of Contents
Key Takeaways
Point | Details |
Importance of Vulnerability Scanning | Regular vulnerability scanning is vital for protecting digital infrastructures by proactively identifying and remediating security weaknesses. |
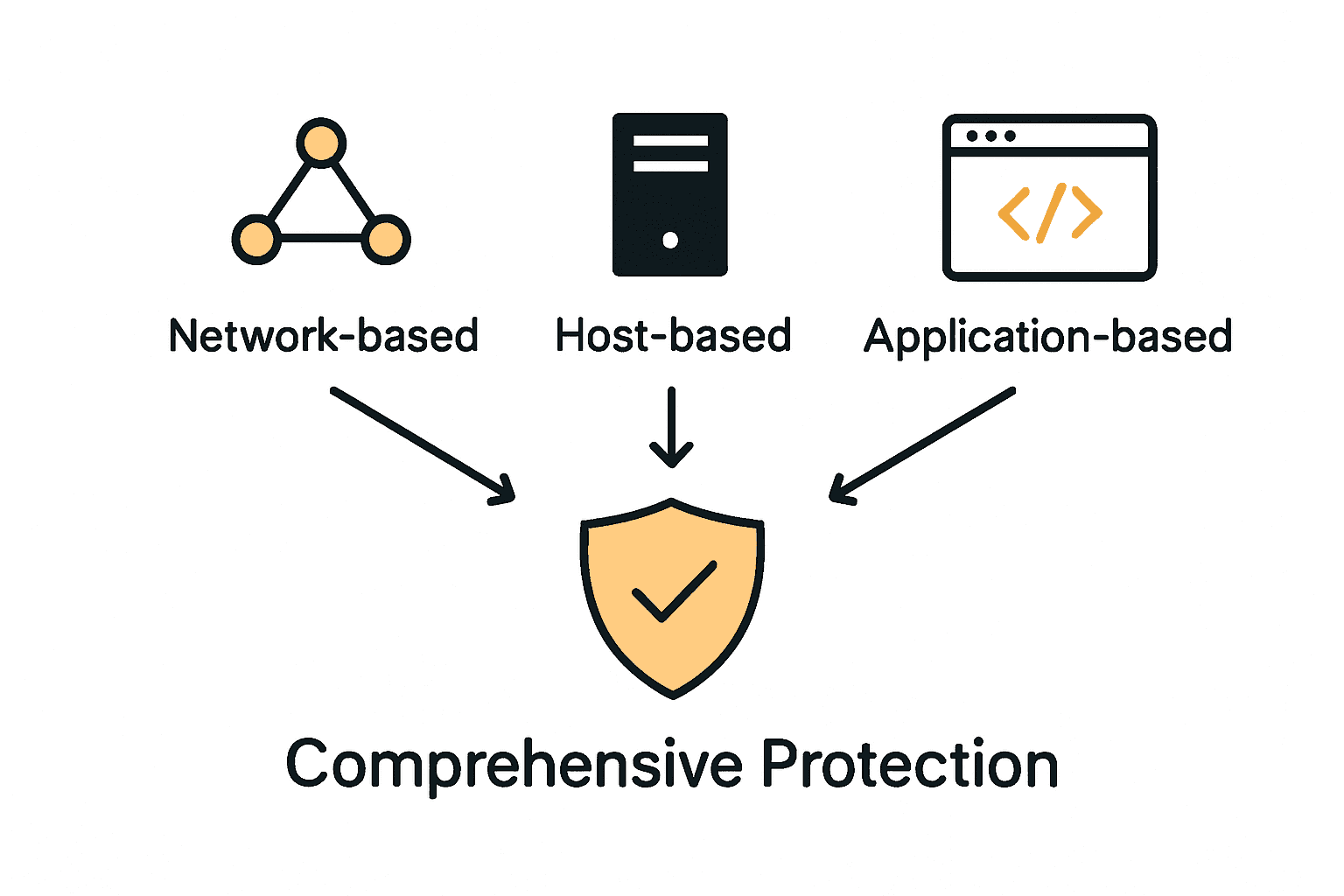
Types of Scans | A comprehensive approach involves various scans (network, host, application) to address security issues across all levels of an organization. |
Compliance and Regulatory Support | Routine vulnerability assessments help organizations meet compliance standards and demonstrate a commitment to cybersecurity diligence. |
Consequences of Neglect | Skipping regular scans increases the risk of cyber attacks, potential financial losses, and significant operational disruptions for businesses. |
What Is Vulnerability Scanning and Why It Matters
Imagine your business’s digital infrastructure as a complex fortress with multiple potential entry points. Vulnerability scanning is like having a dedicated security guard systematically checking every wall, window, and door for potential weaknesses before attackers can exploit them. According to gov.uk, vulnerability assessments help organisations proactively identify and address potential security issues before they become critical threats.
At its core, vulnerability scanning is a systematic process of examining computer systems, networks, and applications to detect security flaws, misconfigurations, and potential points of compromise. As security-guidance.service.justice.gov.uk explains, this process involves comprehensively scanning systems to ensure vulnerabilities are identified and remediated promptly, maintaining overall system integrity.
Key aspects of vulnerability scanning include:
Automated detection of security weaknesses
Comprehensive assessment of network and system configurations
Identification of outdated software and potential entry points
Prioritisation of discovered vulnerabilities based on potential risk
Generation of detailed reports for targeted remediation
For small and medium-sized enterprises (SMEs), vulnerability scanning isn’t just a technical exercise - it’s a critical business protection strategy. By regularly scanning your digital infrastructure, you can prevent potential breaches, protect sensitive data, maintain customer trust, and demonstrate your commitment to robust cybersecurity practices.

Think of it as a proactive health check for your digital ecosystem, ensuring that potential vulnerabilities are caught and addressed before they can cause significant damage.
Types of Vulnerability Scans for UK Businesses
Understanding the different types of vulnerability scans is crucial for comprehensive cybersecurity protection. According to ncsc.gov.uk, vulnerability scanning can be categorised into network-based, host-based, and application-based scans, each targeting specific aspects of an organisation’s digital infrastructure to identify potential security weaknesses.
Network-based scans examine the entire network infrastructure, identifying potential vulnerabilities in routers, switches, firewalls, and other network devices. These scans help businesses detect misconfigurations, outdated firmware, and potential entry points that external attackers might exploit. Host-based scans dive deeper, focusing on individual computer systems, servers, and endpoints to assess operating system vulnerabilities, missing patches, and potential internal security gaps.
Additionally, security-guidance.service.justice.gov.uk recommends implementing a combination of internal and external vulnerability scans to comprehensively assess an organisation’s security posture. Application-based scans provide another critical layer of protection by examining web applications, databases, and software systems for potential coding vulnerabilities, security misconfigurations, and potential points of compromise.
Types of vulnerability scans include:
External network scans: Identifying vulnerabilities visible from outside the organisation
Internal network scans: Assessing risks within the organisation’s network
Web application scans: Checking for security flaws in online systems and platforms
Database scans: Identifying potential security weaknesses in data storage systems
Wireless network scans: Examining potential vulnerabilities in Wi-Fi and wireless infrastructure
For UK businesses, especially small and medium-sized enterprises, implementing a comprehensive vulnerability scanning strategy means going beyond a single type of scan. By combining different scanning approaches, organisations can create a robust, multi-layered security framework that proactively identifies and addresses potential vulnerabilities before they can be exploited by malicious actors.
How Vulnerability Scanning Supports Compliance
For UK businesses navigating increasingly complex regulatory landscapes, vulnerability scanning has become a critical tool in demonstrating cybersecurity diligence. According to gov.uk, regular vulnerability assessments are essential for meeting compliance requirements, showcasing an organisation’s proactive commitment to identifying and mitigating potential security risks.
Compliance frameworks like Cyber Essentials, PCI DSS, and GDPR demand rigorous security practices, and vulnerability scanning provides a structured approach to meeting these standards. security-guidance.service.justice.gov.uk emphasises that implementing routine vulnerability scanning helps organisations adhere to compliance frameworks by ensuring security vulnerabilities are promptly identified and addressed, thereby reducing the risk of potential data breaches.
Key compliance areas supported by vulnerability scanning include:
Demonstrating ongoing security monitoring
Providing documented evidence of risk management
Meeting regulatory requirements for security assessments
Identifying and remediating potential compliance gaps
Maintaining an auditable security posture
Beyond mere box-ticking, vulnerability scanning transforms compliance from a bureaucratic exercise into a meaningful security strategy. By systematically identifying and addressing potential weaknesses, businesses can not only satisfy regulatory requirements but also build genuine, robust cybersecurity defences. For small and medium-sized enterprises, this approach means turning compliance into a competitive advantage - proving to clients, partners, and regulators that your organisation takes cybersecurity seriously and is committed to protecting sensitive data.
Risks of Skipping Regular Vulnerability Scans
In the rapidly evolving landscape of cybersecurity, neglecting vulnerability scans is akin to leaving your digital front door wide open. According to ucisa.ac.uk, failing to conduct regular vulnerability assessments can lead to undetected security flaws that dramatically increase the risk of cyber attacks and potentially catastrophic data breaches with severe financial and reputational consequences.
security-guidance.service.justice.gov.uk warns that skipping regular vulnerability scans may result in prolonged exposure to known vulnerabilities, essentially creating an open invitation for malicious actors to exploit your systems. Unaddressed vulnerabilities become strategic weaknesses that cybercriminals can systematically probe and leverage, transforming your organisation’s digital infrastructure into an easy target.
Potential risks of irregular or non-existent vulnerability scanning include:
Increased likelihood of successful cyber attacks
Potential financial losses from data breaches
Compromised customer and stakeholder trust
Potential legal and regulatory penalties
Extended system downtime during recovery
Substantial incident response and remediation costs
For small and medium-sized enterprises, the consequences of overlooking vulnerability scanning can be particularly devastating. A single undetected security flaw could potentially compromise entire business operations, leading to data theft, financial losses, reputational damage, and in worst-case scenarios, complete business disruption. Investing in regular, comprehensive vulnerability scanning is not just a technical recommendation - it’s a critical business survival strategy in today’s interconnected digital ecosystem.
Best Practices for Ongoing Vulnerability Management
Establishing a robust vulnerability management strategy requires more than occasional scanning. According to gov.uk, this process involves integrating continuous scanning, timely remediation, and embedding security practices directly into the software development lifecycle, creating a proactive and dynamic approach to cybersecurity.
security-guidance.service.justice.gov.uk emphasises a structured approach to vulnerability management that encompasses comprehensive asset identification, detailed risk assessment, and strategic vulnerability prioritisation. This methodology ensures that organisations don’t just identify potential security weaknesses, but systematically address them based on their potential impact and likelihood of exploitation.
Key best practices for ongoing vulnerability management include:
Conduct regular, automated vulnerability scans
Maintain an up-to-date inventory of all digital assets
Prioritise vulnerabilities based on potential risk and business impact
Establish clear remediation timelines and responsibilities
Implement continuous monitoring and tracking
Develop a repeatable patch management process
Create incident response and escalation protocols
For small and medium-sized enterprises, effective vulnerability management is not a one-time event but a continuous journey. By adopting a proactive, systematic approach, businesses can transform vulnerability scanning from a reactive security measure into a strategic risk management tool. This approach not only protects against potential cyber threats but also demonstrates a commitment to robust cybersecurity practices that can enhance customer trust and potentially become a competitive advantage in an increasingly security-conscious marketplace.
Take Control of Your Vulnerability Scanning with Freshcyber
Vulnerability scanning is essential for protecting your business from costly cyber attacks and meeting strict compliance requirements. The challenge for many SMEs is managing ongoing scans, timely remediation, and continuous monitoring without overwhelming busy teams. Freshcyber understands these pressures and offers practical, hands-on support tailored to your needs. We help you stay ahead by providing continual vulnerability management that aligns perfectly with your regulatory obligations such as Cyber Essentials, PCI DSS, and ISO 27001.

Don’t leave your business exposed to unnecessary risks or last-minute audit panic. Visit Freshcyber now to discover how our expert consultancy and our Cyber Elite service can automate your vulnerability scanning and certification processes. Benefit from clear guidance, proactive vulnerability identification, and peace of mind all year round. Take the first step today and secure your business’s digital future with Freshcyber’s Cyber Essentials support.
Frequently Asked Questions
What is vulnerability scanning?
Vulnerability scanning is a systematic process that examines computer systems, networks, and applications to identify security flaws, misconfigurations, and potential points of compromise before they can be exploited by attackers.
Why is vulnerability scanning important for SMEs?
For small and medium-sized enterprises, vulnerability scanning is crucial as it helps prevent data breaches, protects sensitive information, maintains customer trust, and demonstrates commitment to cybersecurity practices.
What types of vulnerability scans are available for businesses?
The main types of vulnerability scans include network-based scans, host-based scans, application-based scans, external and internal network scans, web application scans, database scans, and wireless network scans, each targeting specific areas of an organization’s digital infrastructure.
How can vulnerability scanning support compliance requirements?
Vulnerability scanning assists businesses in meeting compliance frameworks by regularly identifying and addressing security vulnerabilities, providing documented evidence of risk management, and demonstrating ongoing security monitoring, ultimately reducing the risk of data breaches.
Comments